// HI, I’M David, A…
{” _Cybersecurity & Cloud Engineer..”}
{/}
<about_me>
…A Cybersecurity & Cloud Engineer based in Ghana. I specialize in vulnerability assessment, exploit validation, and cloud infrastructure hardening. I help local and global teams build secure, scalable, and resilient systems.
…I have 5 years of experience in IT, spanning help desk support, cybersecurity training, internships, and building advanced home labs.
…From resolving system issues in help desk roles to validating exploits in my labs, I’ve built resilience and adaptability. Through structured training and internships, I gained exposure to vulnerability assessment, patch validation, and incident response — preparing me for real‑world cybersecurity challenges.
(!)
<portfolio>
…Hands-on security, cloud, and identity projects showcasing practical experience in threat detection, automation, and enterprise endpoint management.
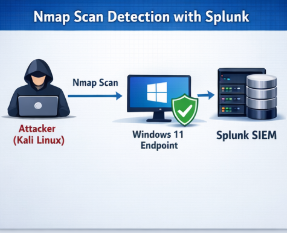
This lab demonstrates a SOC-style monitoring setup where endpoint and network activity is collected and analyzed in Splunk. Simulated reconnaissance activity is detected through log correlation, triggering alerts that highlight suspicious scanning behavior against a Windows endpoint.
Focus areas:
SOC monitoring, log analysis, alert creation, network visibility
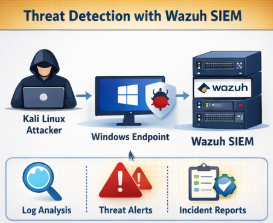
A centralized threat detection lab using Wazuh to monitor endpoint behavior and security events. Logs from a Windows system are analyzed and correlated to identify suspicious activity, providing hands-on experience with SIEM workflows and alert-driven detection.
Focus areas:
Threat detection, endpoint monitoring, SIEM operations, security analytics
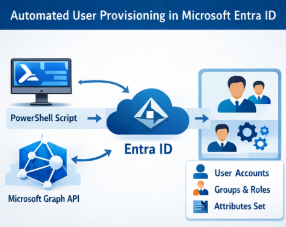
This project showcases automated identity management using PowerShell and Microsoft Graph. User accounts are provisioned in Microsoft Entra ID with predefined attributes, groups, and roles, improving consistency and reducing manual administrative effort.
Focus areas:
Identity automation, Entra ID, PowerShell, Microsoft Graph
{#}
<services>
…Security-focused services designed to improve visibility, strengthen identity controls, and protect enterprise endpoints.
{“_detect_threats “}
{“_secure_identities “}
{“_protect endpoints “}
{*}
<contact_me>
…Get in touch to discuss cybersecurity projects, services, or collaboration opportunities..
